Together, we can reinvent your business
As cloud migration and digital transformation reach new levels of ubiquity, it’s clear that multi-cloud and hybrid cloud environments allow for greater speed, agility, and security. However, multiple clouds mean more significant challenges. One of the biggest hurdles to arise is how to secure legacy applications consistently across clouds and on-premises.
The reality is that modern security tools such as multi-factor (MFA) or passwordless authentication can’t be used on legacy or non-standards-based apps. Making apps secure in the cloud(s) traditionally means manually recoding each one, which is time-intensive and costly and redirects valuable IT resources from innovation.
A critical part of going multi-cloud means managing the new identity silos that come with each cloud. Distributed identity empowers you to manage identity and policies across multiple clouds consistently.
We call this new distributed identity model an identity fabric.
Comprehensive Identity Fabric
What is an identity fabric?
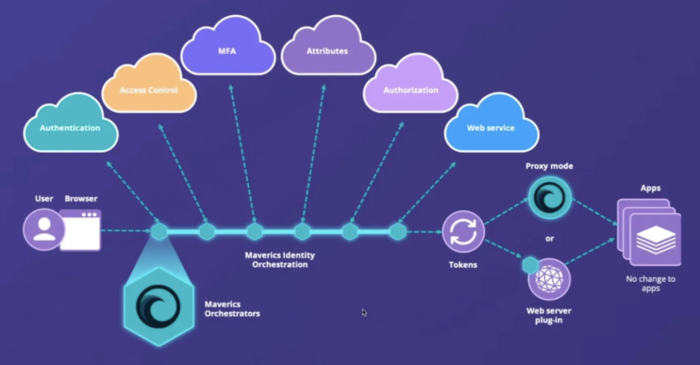
An identity fabric is an abstraction layer in a multi-cloud identity management framework and is part of Identity Orchestration software.
The identity fabric uses orchestration to manage multiple identity domains on multiple clouds.
It also uses abstraction to:
- Manage identity across any IDP (both on-premises and cloud-based)
- Access policies across cloud vendors
- Avoid rewriting apps to speak modern protocols
- Offer a no-code integration that eliminates custom coding
In other words, an identity fabric enables the orchestration of distributed environments, allowing for consistent identity and access to policy management across the network.
How does an identity fabric work?
It starts with the abstraction layer, which inventories and maps the elements of the extended identity system across multiple clouds. As a connecting layer that enables the orchestration of disparate environments, an identity fabric has interwoven threads connecting legacy infrastructures with cloud-based assets. The identity fabric enables consistent identity and access policy management for multi-cloud and hybrid clouds.
The identity fabric abstraction layer unifies distributed identity providers and infrastructures like MFA, directories, databases, APIs, authentication, and authorization providers. Developers can use a single abstracted API for the entire range of connected systems, enabling consistent identity and access across multiple clouds and vendors.
With no-code or low-code integration, an identity fabric eliminates the need to custom-code identity into apps for cloud deployment. IT teams can use a configuration approach to ‘wire’ apps and identity, making it possible to switch one identity provider out for another easily and without coding. Or, they can roll out a new identity service — like passwordless, for example — to apps without rewriting the app.
Why is an identity fabric needed in multi-cloud? What problems does it solve?
Navigating identity and access management (IAM) within multi-cloud and hybrid cloud environments can feel like steering through a dense fog. Without clear visibility, risks increase – including security breaches and costly consequences.
An identity fabric breaks identity lock-in, unifies fragmentation, reduces risk, and enables agility and choice across clouds.
It’s like your lighthouse, allowing you to see through the complexity to solve crucial problems, such as:
Identity lock-in
Identity vendor lock-in is common in IAM and can add an extra layer of frustration for IT leaders seeking to update their systems due to policy compliance reasons or other business drivers.
Identity lock-in occurs when apps integrated with legacy identity systems use outdated ‘cookie’ sessions. Moving off this model requires rewriting apps to work with a new identity system, taking months of developer time. In turn, this locks organizations into the legacy platform that legacy identity runs on, preventing apps from moving to the cloud.
Fragmentation & silos
Organizations using more than one cloud must contend with identity fragmentation. Fragmented identity silos and manual IAM for critical infrastructure puts constraints on your business.
An identity fabric enables consistent identity and access policies to be implemented across disparate clouds and platforms.
Cybersecurity threats
Cybercriminals are getting bolder and more sophisticated. But they still go after the low-hanging fruit first — even criminals know there’s value in keeping it simple. The 2023 Verizon Data Breach Investigation Report found that 86% of data breaches involved the use of stolen credentials. Weak passwords and poorly protected passwords are arguably the weakest links.
With the distributed nature of the cloud — and now multiple clouds — a new approach to managing identity is needed.
While there’s no substitute for robust threat detection systems, the capacity to instantly deploy IAM updates and enforce policy changes ensures that vulnerabilities are quickly addressed. Cybersecurity and IAM are now intrinsically connected across all areas of an organization.
Agility
An identity fabric enables organizations to decouple their infrastructure from their apps, making it possible to easily move apps and workloads across clouds using whatever identity system makes the most sense for the use case.
Benefits of using a distributed identity fabric
We’ve addressed how an identity fabric directly addresses the challenges of fragmented identities, vendor lock-in, and security vulnerabilities. Let’s take a further look at some of the other key benefits an identity fabric brings to an organization.
1. Fix identity fragmentation
An identity fabric can help you integrate silos of identity across different cloud platforms and on-prem systems, enabling you to enforce consistent policies across multiple cloud platforms.
2. Break vendor lock-in and enjoy agility and choice
With an identity abstraction layer that enables you to use the cloud platform and identity solution of your choice while eliminating the need to rewrite apps when migrating identity systems.
3. Reduce costs for identity
Reduce the costs of rewriting apps to work with different identity systems. Reduce costs for moving platforms and integrating identity with apps. Save millions in measurable hard costs.
4. Speed up identity projects
Automate identity workflows like authentication, access control, migration, and last-mile integration across different identity platforms—on-prem and in the cloud. Using automation and orchestration instead of custom code can cut project timelines by more than 85%. Speed work-from-home deployments by rapidly making apps available outside the firewall.
5. Zero-touch deployments
Drop-in implementation means no disruptions to apps, infrastructure, or user experience. Zero-code connector integrations eliminate custom code.
6. Distributed, multi-cloud identity support
Support multi-cloud distributed apps that require consistent identity across multiple clouds.
7. Improve security by eliminating identity silos
Tapping advanced security features like MFA, passwordless, GDPR privacy, etc.
Protect your infrastructure against cyberattacks with Identity Fabric Immunity
Identity fabric immunity refers to the resilience of your identity infrastructure against targeted cyberattacks and internal vulnerabilities. Resilience stems from the decentralized nature of the fabric, coupled with robust security mechanisms.
Key Identity Fabric Immunity Principles:
- Zero Trust: Continuously verifying user identity and privileges.
- Least Privilege: Granting only the minimum access required to perform tasks.
- Multi-Factor Authentication (MFA): Enforcing multiple verification factors.
- Context-Aware Access: Considering device, location, and behavioral patterns.
- Continuous Monitoring: Detecting and responding to anomalous activities.
How does an identity fabric strengthen immunity?
An identity fabric, through its architecture and features, enables the implementation of these principles across a diverse IT and cloud landscape. It also provides the tools to centralize policies, automate access control, and enforce security consistently across your entire infrastructure — reducing human error and limiting the impact of any single point of compromise.

Why Choose Identity Fabric
- Proactive defense against emerging threats.
- Tailored solutions that align with your goals and industry.
- Increased organizational resilience and readiness.
- Support for achieving and maintaining regulatory compliance.
Our Identity Fabric Process
Our cybersecurity consulting process is designed to provide a holistic approach to protecting your organization. From assessing your current security landscape to implementing tailored solutions and ensuring continuous improvement, we guide you through every step of the journey. With a focus on understanding your unique needs and addressing vulnerabilities, our methodology ensures your business stays resilient against evolving threats while aligning with your operational goals.

Understanding Your Security Needs and Goals
We start by thoroughly assessing your current security landscape, including infrastructure, systems, and processes. We work to understand your business objectives and industry-specific compliance requirements to ensure our solutions align with your operational goals.

Uncovering Gaps and Vulnerabilities
Once we have a clear picture of your environment, we conduct a detailed analysis to identify gaps and vulnerabilities. This step involves evaluating potential risks in your systems, processes, and policies to uncover areas that could expose your organization to cyber threats.

Crafting a Tailored Security Strategy
Based on our findings, we develop a comprehensive strategic security framework tailored to your unique needs. This plan includes actionable recommendations, technology roadmaps, and priority areas to address potential weaknesses while supporting long-term resilience.

Implementing Solutions for Stronger Protection
During the execution phase, we provide end-to-end support for the implementation of security measures. This includes deploying necessary technologies, configuring systems, and delivering training to empower your team with the skills and knowledge to maintain a strong security posture.

Ensuring Continuous Security Improvement
Cybersecurity is a continuous journey. Our experts work with you to monitor your security environment, refine strategies, and adapt to emerging threats. We help you implement ongoing improvements to ensure your defenses remain robust and effective.
Take the First Step Toward Enhanced Cybersecurity
Protect your business, safeguard your data, and build resilience against evolving threats with FalconRock’s expert cybersecurity solutions.
Cybersecurity Consulting in Action
Our Identity fabric services are designed to offer a consistent view and user experience across applications, improving security posture with real-time behavioral risk-based.
McKesson Healthcare, for 2024, reported revenues of $309 billion and employed approximately 51,000 people. McKesson partnered with IBM to develop the McKesson Performance Advisor (MPA), a clinical-based, business predictive analytics/intelligence software solution.
Harvard Pilgrim Health Care (HPHC), as of 2023 reported annual revenues of approximately $2.23 billion, aimed to enhance the CASR II Datawarehouse with a Strategic End-to End Assessment. This project established the strategy and comprehensive requirements the CIO needed to define, develop, and operationalize all business and technical procedures to ensure end-to-end reliability and recoverability of data exchange and integration.
Biogen, a leading biotechnology company, As of 2023, Biogen reported annual revenues of approximately $9.836 billion with about 7500 employees, aimed to enhance its Commercial IT data warehouses to improve data management, reporting capabilities, and overall operational efficiency to support the Asia-Pacific (APAC) region and the US business unit.